
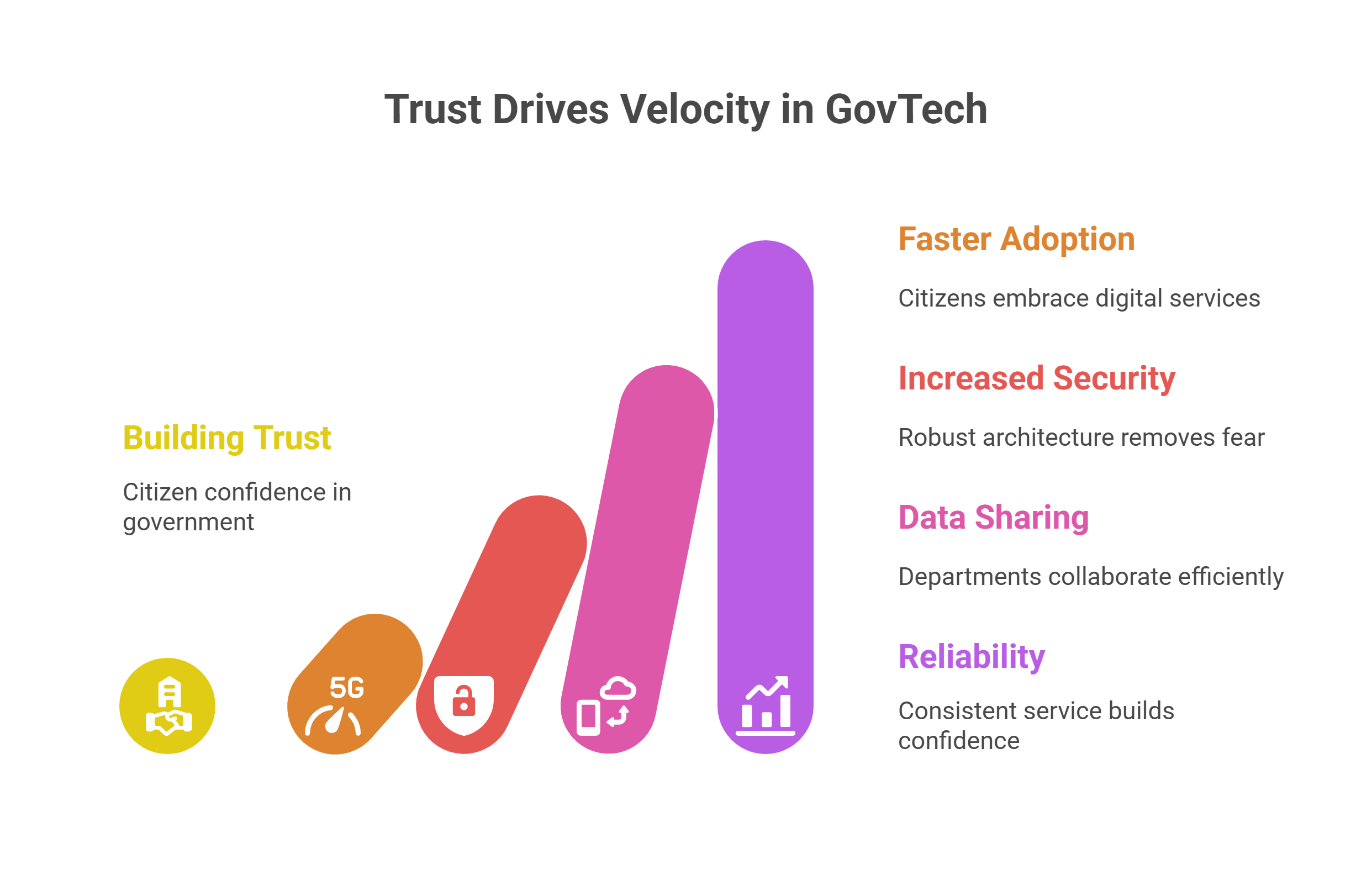
When Aadhaar was launched in 2010, it was more than a number- it was vision merged with ambition to create a unique identity for all. Notably, the first people to get their Aadhaar cards were 1000 villagers from Tembhali in Maharashtra. It was no trivial event as the entire village got a makeover. In a year of its first roll out, around 100 million people had enrolled for Aadhaar. And, in the years that have rolled since then, we realize how it has emerged as the disruptor in citizen-centric governance. Governments are leveraging people’s demographics embedded in Aadhaar for more efficient targeting of schemes and their implementation as well as disbursement of funds to beneficiaries. Riding on strengths like data encryption and foolproof authentication, governments have seeded Aadhaar of beneficiaries with flagship programmes like old age pension, MGNREGA, Public Distribution System (PDS) and farmers’ registration & subsidy transfer to enhance quality of outcomes.
How Aadhaar Act has shown the way
The operations of SRDHs got legal teeth with the amendment to Aadhaar (Targeted Delivery of Financial and Other Subsidies, Benefits and Services) Act, 2016 concomitant with amendments to the archaic Indian Telegraph Act, 1885 and the Prevention of Money-laundering Act, 2002. The umbrella legislation- Aadhaar and Other Laws (Amendment) Ordinance Amendment, 2019 has dispelled concerns on the misuse of Aadhaar. Entities can perform authentication only when they are compliant with the standards of privacy and security mandated by UIDAI. The amendment has also proposed deletion of the contentious Section 57 of the Aadhaar Act which allowed sharing of data with private entities.
SRDHs – The Force Multipliers to Seamless G2C services
SRDHs have led to accurate identification of beneficiaries and enabled government departments to verify and weed out erroneous as well as fictitious data from their records. It marks a new epoch in more responsive citizen service delivery with exclusion of ghost beneficiaries. The SRDH ecosystem has eased integration of Aadhaar with the National Population Register (NPR) with departmental utility databases on a real time basis. States have gone beyond. Say for instance, Andhra Pradesh and Haryana have strengthened capabilities of their data hubs with GIS mapping of households linked with all activities from birth to death. So, for any bulk authentication to register myriad beneficiaries for any government to citizen (G2C) intervention, SRDH has offered a robust framework. With such a rich data repository and Aadhaar backed identity verification, any government agency can conveniently identify and disburse to beneficiaries.
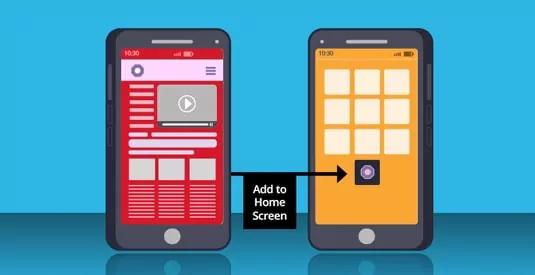
SRDHs have smoothened the digital delivery of services, easing the bipartite interaction between government and citizens. With the promise of emerging technologies like facial recognition, digital authentication can take a leap forward, nudging India closer to its vision of a $1 trillion ‘Digital Economy’ by 2025.
The author is Priyadarshi Nanu Pany, founder & CEO of CSM Technologies. This article was originally published on his LinkedIn profile .



































We will verify and publish your comment soon.